Today’s global architecture of communication is on the verge of a seismic change, shifting away from the hardware limitations of today to a much more fluid, software-based tomorrow. For years, the plastic SIM card ruled the roost and held us safe with an identity attached to a phone number and a location. The plastic SIM card for decades has been the main gateway to our digital self, securely locking our phone numbers into a single geographical location and its silicon chip. But in an era of increasing privacy concerns and an elastic need to meet the challenge of moving across borders, the old model is looking tired.
The advanced platforms, such as GetTempNumber.com, are becoming more popular with modern users, as they use them for managing their digital footprint. The service offered here is wide-ranging and gives users one-time verification SMS for immediate use, and prepares them to use virtual numbers for personal and business use. Such services provide flexibility and security that a traditional SIM card can’t match since the phone number is not linked to the physical device.
The Structural Limitations of Physical SIM Cards
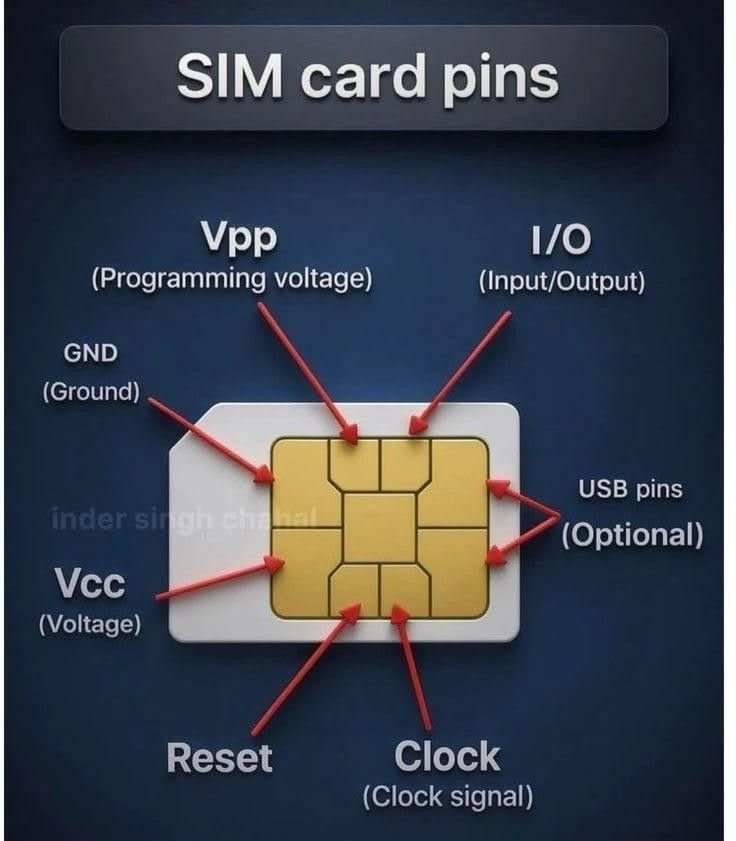
The advantages of a virtual number are only seen with a closer look at the physical SIM’s shortcomings. Firstly, understanding the advantages of a virtual number requires an understanding of the limitations found in the physical SIM. Simply put, a SIM (Subscriber Identification Module) card is a physical key. It can also be misplaced, lost, stolen, or physically damaged, just like any physical key.
https://i.pinimg.com/736x/0f/bc/1e/0fbc1ee52c35fe447936602add6a5d19.jpg
The SIM Swap Vulnerability
The SIM swapping scam is one of the biggest security risks faced in 2026. The attacker goes to a mobile carrier and tricks it into porting a victim’s mobile phone number to a SIM card in the attacker’s possession. If the attacker is in control of the physical line, then they may be able to reset passwords for bank, social media, and email accounts using SMS Two Factor Authentication (2FA). Since the physical SIM card is part of a centralised carrier admin system, the user is usually the first to know their identity has been compromised.
Geographic Lock-in and Roaming Fees
The problem with physical SIM cards is that they’re certainly local. Issued by a particular carrier in a particular country. You have to either pay over-the-lodger for a cross-border call or you have to go searching for a local plastic card – submit passports, wait for it to be activated, and deal with little fragments of plastic. This “hardware-first” model is becoming more and more unsuitable for digital nomads and companies that run internationally.
Hardware Dependency
The loss of your phone means the loss of your number – and all of the 2FA-protected services. If your phone breaks or gets stolen, your number is effectively lost, and so are all 2FA-protected services until you have a replacement phone with a new number. In a hectic work world, this disruption can have devastating effects.
The Virtual Numbers Games: Security, Scalability, and Privacy
Virtual numbers, like those returned by the GetTempNumber service, work on a completely different basis. The chip doesn’t live in the computer, but in the cloud it remains. This small change in architecture will address almost every issue with the traditional SIM.

https://i.pinimg.com/736x/6f/51/e9/6f51e9ef707bc7c3b58ae91d5a5ffb37.jpg
Enhanced Privacy through Compartmentalization
The strongest argument for a virtual number, however, is the idea that one could isolate their virtual space so that intrusion into it would not be a problem one has to deal with. The era you’re in is what’s known as the “data breach” era, where your main phone numbers are often dumped in bulk from large corporate data breaches. If your primary number is added to a spam list, then that number remains on the list permanently.
When you register for an account just one time (such as for a novel social media App, or a dating profile), you put together a safeguard. If this service is not satisfactory, your fundamental personal number is not affected. It isn’t something that is simply convenient; it’s a crucial part of modern-day-to-day digital hygiene.
Infinite Scalability
The “one phone, one number” is a significant limitation for entrepreneurs and content creators. The virtual number service enables you to control multiple lines in various areas from one dashboard.
Case Study: A freelance developer from Ukraine wants to check the accounts of two US-based Stripe accounts and the Amazon seller profile of a seller from the UK. They don’t need to deal with three different physical phones or costly roaming SIMs as they can use a GetTempNumber service to manage SMS verifications without a second thought, and even turn those numbers into a long-term business asset.
Virtual numbers are software-based, thus not device-dependent. View SMS messages or control your phone calls on your laptop, tablet, or another phone. If your main phone happens to drop into a lake, then you don’t lose your identity. All you need to do is log on to your service from another device and then get back to your work.
Comparative Analysis: Physical vs. Virtual
Let’s examine, in more detail, the essential distinctions between these two technologies concerning the present situation of the 2026 tech world.
| Feature | Physical SIM Card | Virtual Number (GetTempNumber) |
| Activation Time | Minutes to hours (needs shipping or store visit) | Seconds (instant digital delivery) |
| Privacy Level | Low (tethered to ID and physical location) | High (protects primary identity) |
| Travel Utility | Poor (high roaming / manual swap required) | Excellent (works globally via Internet) |
| Security | Vulnerable to SIM swapping | Encrypted cloud access / no physical theft risk |
| Hardware Requirement | Specific SIM slot or eSIM chip | Any device with an Internet connection |
| Cost Control | Monthly contracts or high roaming | Pay-per-use, or transparent flat rates |
If virtual vs physical sim were just convenient, then here are some practical examples of why it is a strategic decision instead.
Safeguarding Financial Assets
Notably, a lot of cryptocurrency exchanges and regular banks are still using SMS as their 2FA. Using your primary number (the one that is usually associated with your business name and your address in a public record), on the other hand, is a liability. Sophisticated investors have a virtual number for their investment accounts that they don’t use for social media or the public sphere. Attacks like this make it exponentially more difficult for hackers to attack the account because they can’t be certain of what number to try swapping.
Global Market Expansion
If a Canadian business is seeking to introduce a new product or service to the UK market, a virtual UK business phone number could be a great solution. This way, they can get questions from customers and check local business websites, such as Google My Business, without having a store or the landline you need to purchase.
Avoiding the “Spam Trap”
Everyone has come across this situation at one time or another; you want to download a whitepaper or use a free tool, and the website requires a phone number. Everyone has been there: you want to download a whitepaper or use a free tool, but the site asks for a phone number. In 90% of cases, that number is sold to telemarketers. With a one-time SMS service from a provider such as GetTempNumber, you can receive the verification code you require, and then discard the interaction, leaving your personal inbox clean and quiet.
The de-proliferation of numbers is also emerging as another area of the movement towards disposable or modular digital identities. While a VPN helps protect your IP address and encrypted mail services keep your mail secure, virtual numbers are the VPN for telephony.
In today’s landscape of AI-powered spam bots capable of sending out millions of cold calls an hour, the need to rapidly rotate and/or kill a number is a must-have defense method. Traditional carriers, which have 12-month or 24-month contracts, can simply not provide this agility.
Quality SEO Practices and Trustworthiness
Guest articles can be useful in the field of search engine optimisation (SEO) because of the reliability they provide. Google’s recent developments focus on the quality of its E-E-A-T elements: Experience, Expertise, Authoritativeness, and Trustworthiness. We explain the technical details of virtual numbers, like the difference between a VoIP-based number and mobile-allocated virtual lines, and so we write content genuinely useful to the reader.
In addition, over-optimization should be avoided.
The main takeaway from the GetTempNumber may be that the platform is developing into a comprehensive communication tool, but it has an initial functional benefit of supplying one-off codes quickly. The new feature, which lets people buy and keep numbers for their own, long-term use, will help to close the rift between the transient nature of privacy and the enduring digital residency.

https://i.pinimg.com/1200x/fc/30/6a/fc306a63f4c62789e04535ff85a68fd0.jpg
Making the Switch
From travelers seeking to prevent roaming charges to privacy-conscious users wanting to safeguard themselves from SIM cards being snapped, to business people who are going international, the proof is in the pudding: the virtual path is not only an alternative, it’s the better path. Obviously, some services, such as GetTempNumber, are at the forefront of this revolution, and they enable you to surf the Internet securely, privately, and without the burden of clicking through them.
Now that we are looking toward the future, the question isn’t necessarily if you are ever going to use a virtual number; it’s how many you’re going to stick with to maintain a digital life that is secure and organized. The old days when the SIM card still existed, and was always in place, and on-demand time have finally come and gone, and the days when a virtual identity could exist have begun.


